What is DDOS? What are different ways to mitigate DDOS attacks?
- December 7, 2017
- 0
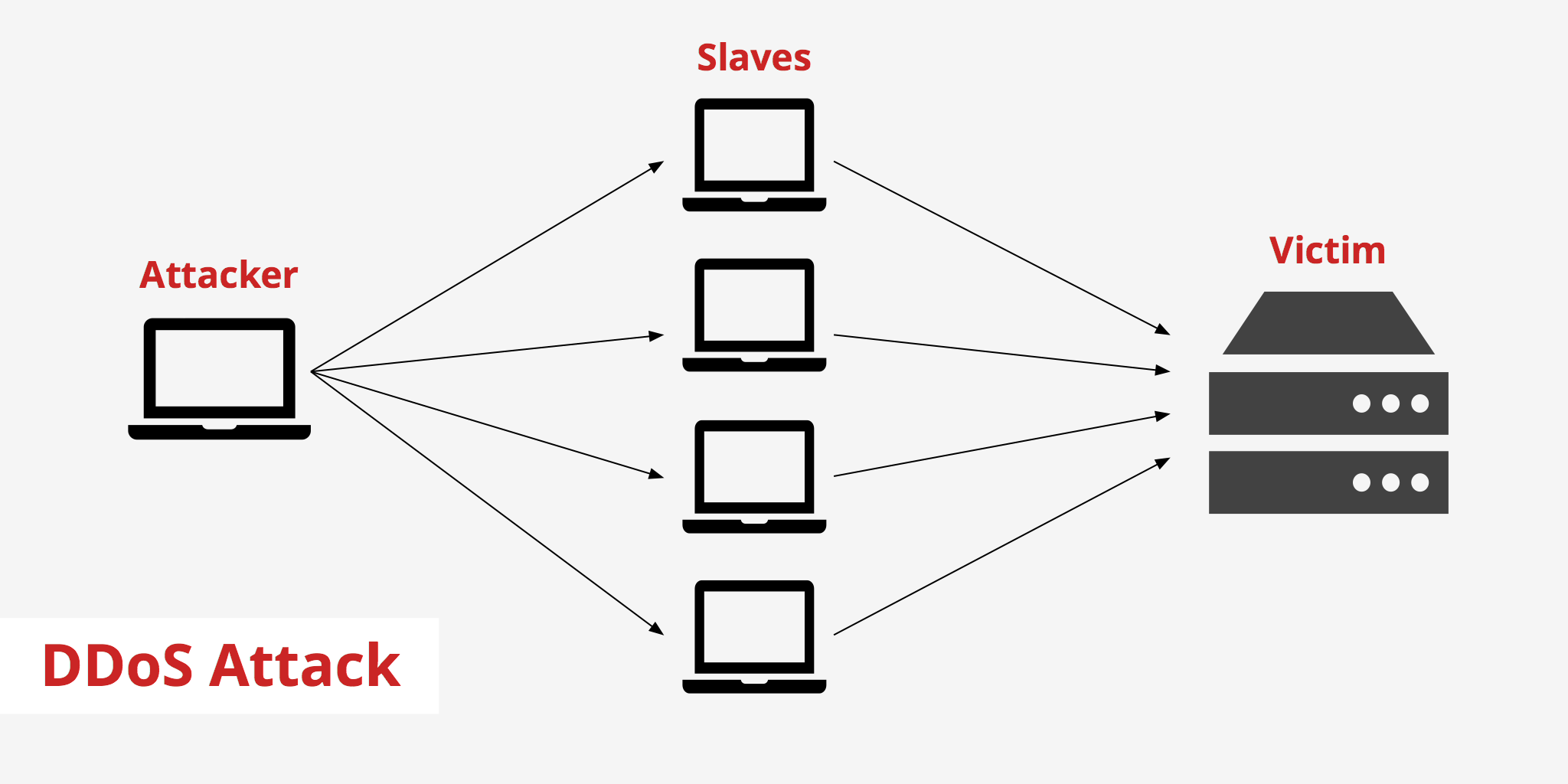
Distributed Denial Of Service (DDOS)
Distributed Denial of Service is a dangerous cyber-attack in which the target (which can either be a server or a website) is forced to indefinitely stop its services available to its legitimate users. It is basically done by flooding the targeted system with fake traffic from multiple resources which causes the targeted system to slow down or even crash down, thereby denying access to its genuine users.
How does DDOS work?
In a typical DDOS threat, the intruder first starts exploiting the susceptibility in one system which becomes the DDOS master. The master system then starts finding similar vulnerable systems by infecting malware or other types of viruses. This network of systems under the control of a DDOS hacker is referred to as BOT. The DDOS hacker then forms a command-and-control server to control the network of BOTS, also called a BOTNET. Once a proper BOTNET is accumulated, the DDOS hacker uses the traffic generated by these compromised devices to flood the targeted domain.
Types of DDOS attacks
-
Network Centric or Volumetric attacks:The targeted system is flooded with packets until the available bandwidth is exhausted.
-
Protocol attacks:The intruder targets the network layer or transport layer protocols by making use of flaws in the protocols to flood targets.
-
Application Layer attack:The intruder floods the application services or databases of the targeted system with an enormous amount of application calls.
Best Practices to be followed to mitigate DDOS attacks
Self-monitor your website statistics:Use web statistics software to monitor the performance of your website. The software generates periodic reports on performance, user load and page views to detect any abnormalities. Also, monitor different attributes of the traffic including IP addresses, a disparity in cookies, HTTP headers and Java footprints. Similarly, keep track of the network statistics and traffic log files to detect any unusual activity.
Increase your bandwidth:It is important to increase the bandwidth of your website as per the usage. This might not completely prevent a DDOS attack but would provide the much-needed buffer time in case the system crashes down. Also keep, your DNS network extra-protected.
Stop Relying on a Firewall to prevent a DDOS attack:A firewall, which has built-in DDOS protection might not suffice to mitigate DDOS attacks. The ideal solution is to have a purpose-built service that scrutinizes excessive traffic before it strikes your firewall or other components of your network. The sole purpose of this solution is to ensure that fake traffic is prevented and applications are accessible to its genuine users.
Include DDOS into your disaster recovery(DR) plan:Every company would have a business continuity or a DR plan in place that puts forth what needs to be done in the event of service interruption or outage. Just include DDOS mitigation into this plan. This prevents any delay in responding to an attack and also assures that your company commits necessary resources for prevention and mitigation.
Be aware of the signs of an attack:
-
Unusual sluggishness in opening files or accessing website
-
Inaccessibility/ unavailability of a particular website
-
A spike in the number of spam emails received
Know your customers and block unexpected transactions:Any occurrences of inbound traffic from areas where you do not have customers might indicate some sort of trouble. Use an anti-DDOS solution that has the feature to restrict overflow of requests that originate from such suspicious locations.
Set up an alert system:Create an alert system that notifies when there is an abnormal traffic or when the server is about to crash or receives a huge amount of SYN packets, or something similar. This might help to block fake traffic and make ways for the legitimate traffic to access your website.
Be aware of any fraud or data breaches or other malicious activity in case a DDOS attack happens
If a DDOS attack happens, be vigilant enough to monitor and make a thorough inspection of your system logs to find out if other malicious activities took place during the attack period. Be extra cautious of your PCI/credit processing environment in case your website supports credit transactions and deploy proper defences at the boundary of your cardholder data environment.
Know who to call in case of a DDOS attack
Anti-DDOS emergency services such as Arbor Networks, Incapsula, Akamai, etc. provide excellent services in Anti-DDOS solution. Reach out to the right provider at the right time.
To summarize, a proper configuration of the network with the right mitigation plans prevents hacking and accessibility of your web services to hackers.